Configure Remote SSH Connection to Server
Get SSH running on your server machine for WLAN
Install OpenSSH
- OpenSSH is usually automatically installed on Ubuntu, but we'll go ahead with the installation commands. This will install openssh-server. You can also run
sudo apt install openssh-server.
$ sudo apt update
$ sudo apt upgrade
$ sudo apt install ssh- Enable and start the SSH service and verify it is running.
$ sudo systemctl enable ssh
$ sudo systemctl start ssh
$ sudo systemctl status sshConfigure SSH in the firewall (UFW)
- For this step, if you want to run your SSH through the default port 22, then enter the following commands and continue to the next section. Otherwise, skip this step and proceed to step 2.
$ sudo ufw allow ssh
$ sudo ufw enableThis will add an allow rule for 22/tcp to your firewall:
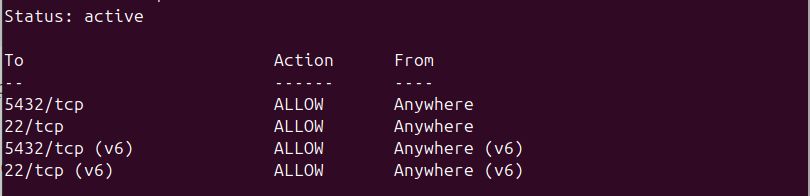
-
Explanation: For added security, we can change the default SSH port. Why does this improve security? Port 22 is the default SSH port on most machines; as such, there are innumerable malicious bots pinging random IP addresses at port 22 to see if they can gain access to a system via SSH. Once they do, they can install a virus, spyware, or malware, or simply steal sensitive information. By changing the default port, we can add a small measure of security against some of the more blatant attack strategies, like bots knocking on port 22.
-
To change your default port, follow this guide.
Attempt to connect to our machine from a client on the same network
- Let's find the ip address of our server machine. If you have not configured a static ip address on your server, your ip will be subject to DHCP and could spontaneously change. To ensure a reliable connection, set up a static ip.
$ hostname -i- If you elected not to change the default SSH port, you can SSH into your server machine in the typical way. A Linux Terminal example:
$ ssh <username>@<ip-address>A Generic GUI example:
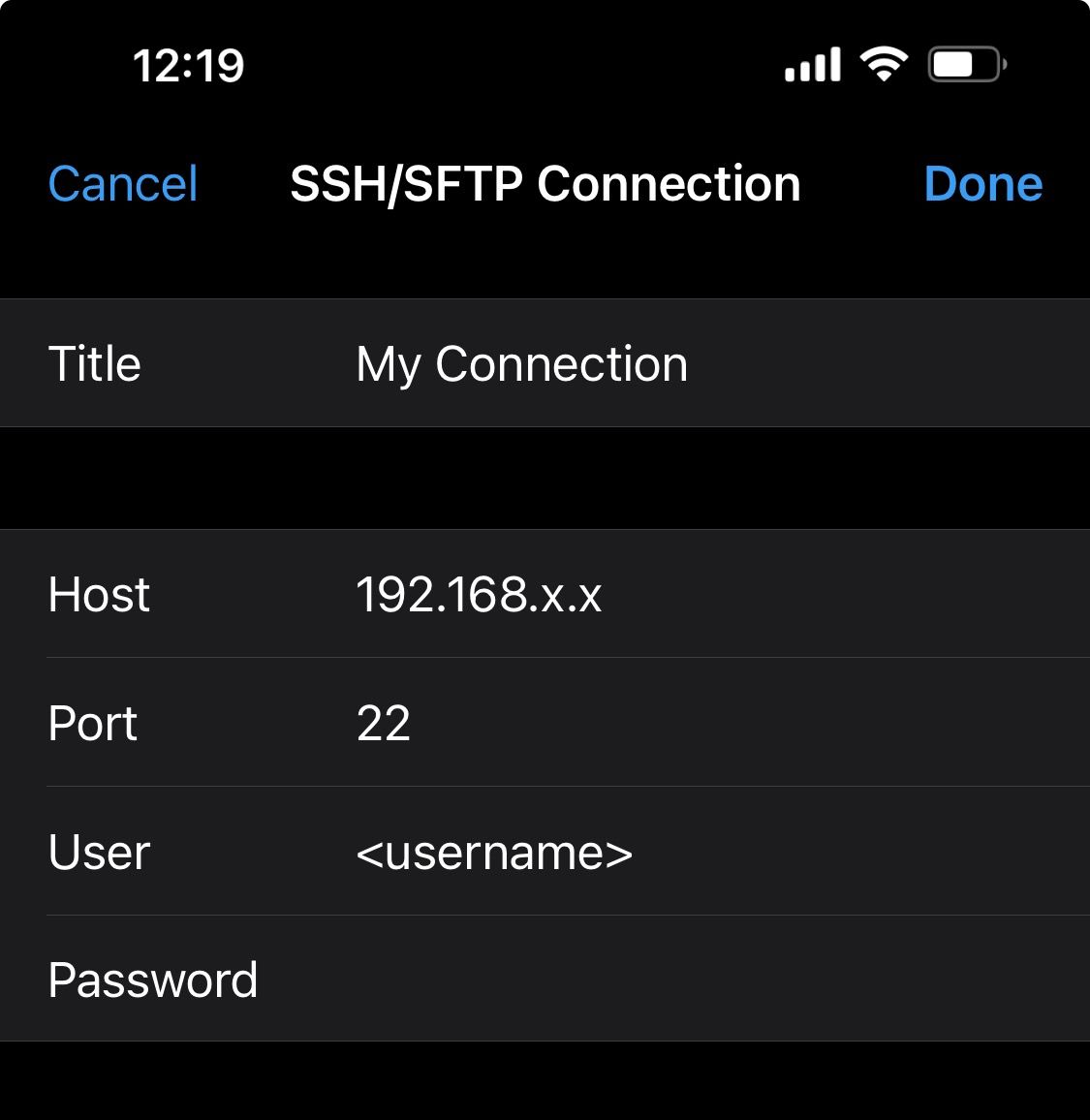
- If you changed the default SSH port, simply indicate it in the command, or specify it in the port field in your GUI.
$ ssh <username>@<ip-address> -p <port>Get SSH running on your server machine for WAN
This section has Get SSH running on your server machine for WLAN as a preqrequisite.
Port Forwarding from the router
-
Some routers may not require this step, i.e. they use a VPN, which doesn't require port forwarding from the router.
-
To set up port forwarding, find the default gateway (probably
192.168.x.x) associated with your router. There are two methods. i. Find it printed on the device itself. ii. Open a terminal windows and run the commandroute -n. I'm using wifi, so the device name I'm looking for will be something likewlan0orwlp. If I were using ethernet, it would probably beeth0. iii. Once you've identified your router, note the ip address underGateway: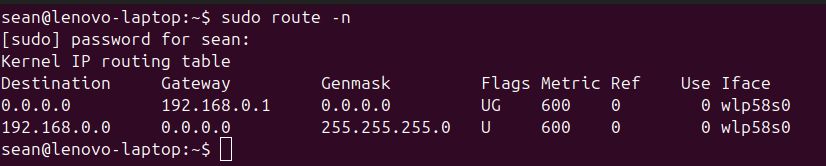
-
Open your browser and enter the IP address into the address bar.
-
The login credentials for you router will be printed on the device.
-
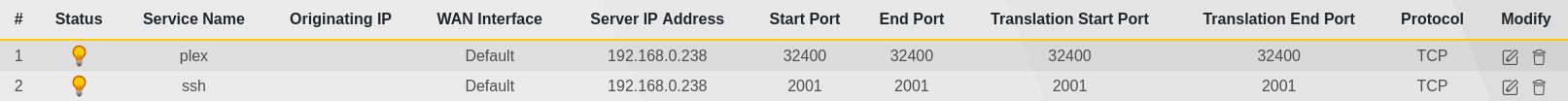
To set up port forwarding for SSH on my router, I navigated to Network Setting, then NAT, where I added the following entry:
Configure a DDNS domain
- At this point in the setup, you can run
curl ip.mein the terminal to find your routers public IP address and use it to remotely access your server withssh <username>@<public-ip-address> -p <port>. However, this is a tenuous connection; since the IP address is subject to change under DHCP (Dynamic Host Configuration Protocol), you may spontaneously lose connection if connected this way. - We can configure a DDNS (Dynamic Domain Name System) domain in the router settings. For my router, I went to Network Setting, DNS, Dynamic DNS.
- Setup of DDNS from here is typically straightforward. We enable it, select a service (I selected www.dynu.net), make an account and domain name, and enter all that information into the fields in Dynamic DNS of our router settings. When creating my domain, I chose to give it a long, obscure name to add just that little extra bit of security.
(Optional) Configure RSA Key Access for SSH
- Using a public and private key pair to authenticate SSH connection between two devices is more secure than merely using a password. It isn't absolutely necessary, but highly recommended.
- follow this walkthrough, setting up ssh key access.
Final Step
- When configuring connections on your devices, create one for WLAN access that uses the static, private IP address of your server, and another for WAN access that uses the DDNS domain your chose.
- You'll need to store the private RSA key somewhere on your client device. In my case, I use the program FE File Explorer to connect, and when configuring my connection, I simply indicated that I would access by key. I was then prompted to point the configuration to the private key, which I had placed in a folder named ssh.
- Done!